Securing Azure Machine Learning: A Deep Dive into Mitigating Silent Threats and Vulnerabilities in Managed MLOps
Introduction
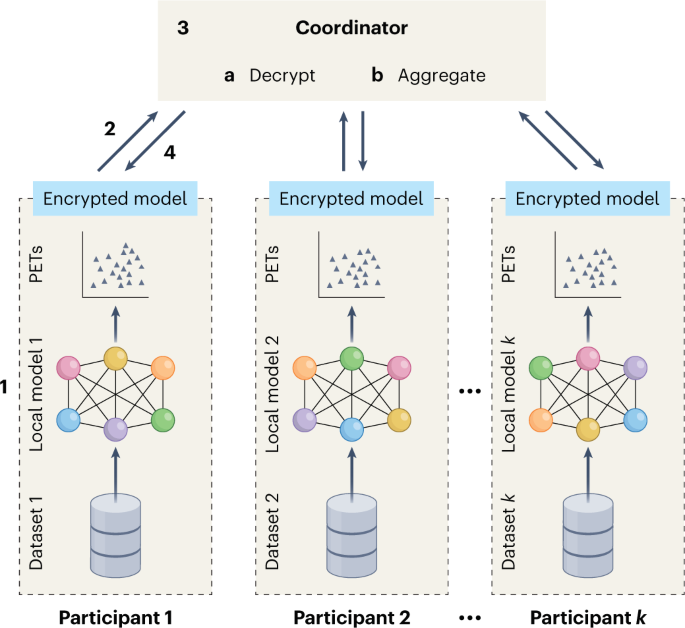
As the adoption of artificial intelligence accelerates across enterprise environments, the security posture of managed machine learning services has become a critical focal point for DevOps and MLOps teams. While platforms like Azure Machine Learning (AML) provide robust tools for the end-to-end machine learning lifecycle, the convenience of managed services can sometimes obscure the underlying attack surface. Recent discussions in the cybersecurity community have highlighted the potential for “silent threats”—vulnerabilities that exist not within the model code itself, but within the configuration of the managed infrastructure, compute instances, and data access patterns.
In the rapidly evolving landscape of Azure Machine Learning News, staying ahead of these threats requires more than just standard firewalls. It demands a comprehensive understanding of how compute resources are provisioned, how identities are managed, and how data flows between storage and training environments. Unlike traditional software engineering, ML systems introduce unique vectors for exploitation, including model poisoning, training data extraction, and unauthorized compute resource consumption (cryptojacking).
This article provides a comprehensive technical analysis of securing Azure Machine Learning workspaces. We will explore the architecture of secure MLOps, contrasting it with developments in AWS SageMaker News and Vertex AI News, and provide practical Python implementations using the Azure SDK v2 to harden your ML environment against unseen vulnerabilities.
Section 1: The Attack Surface of Managed Compute and Network Isolation
One of the most significant risks in managed ML services lies in the configuration of Compute Instances and Compute Clusters. By default, many managed services may provision resources with public IP addresses to facilitate easy access and debugging. However, this convenience creates a direct bridge between the public internet and your internal training environment, potentially exposing sensitive datasets and proprietary algorithms.
Understanding the Risk: Lateral Movement
If an attacker gains access to a Jupyter Notebook running on a Compute Instance (perhaps through a weak token or misconfigured access control), they often inherit the identity assigned to that compute. If that identity has broad permissions—such as access to Azure AI News services, Key Vaults, or storage accounts—the attacker can pivot laterally through the cloud environment. This is a common pattern seen in security research regarding managed services.
To mitigate this, network isolation via Azure Virtual Networks (VNETs) and Private Links is non-negotiable for enterprise-grade security. This ensures that traffic between your workspace, storage, and container registries never traverses the public internet.
Implementation: Configuring a Secure Workspace
The following Python code demonstrates how to programmatically configure a workspace that enforces private access, effectively reducing the exposure of your ML infrastructure. This approach aligns with best practices seen in Google DeepMind News and Meta AI News regarding secure research environments.
from azure.ai.ml import MLClient
from azure.identity import DefaultAzureCredential
from azure.ai.ml.entities import Workspace, ManagedServiceIdentity
# Initialize the ML Client
credential = DefaultAzureCredential()
subscription_id = "YOUR_SUBSCRIPTION_ID"
resource_group = "rg-secure-mlops"
ml_client = MLClient(credential, subscription_id, resource_group)
# Define a secure workspace configuration
# Key security features:
# 1. Public Network Access Disabled
# 2. High Business Impact (HBI) workspace (encrypts local scratch disks)
# 3. User Assigned Identity for granular control
secure_ws = Workspace(
name="aml-secure-prod",
location="eastus",
display_name="Secure Production Workspace",
description="Workspace with Public Access Disabled and HBI enabled",
public_network_access="Disabled",
hbi_workspace=True,
tags={"environment": "production", "security_level": "high"},
identity=ManagedServiceIdentity(
type="system_assigned"
)
)
# Provision the workspace
# Note: In a real scenario, you would also pass existing VNET/Subnet IDs
# and Key Vault resource IDs to fully bind the infrastructure.
try:
ws_result = ml_client.workspaces.begin_create(secure_ws).result()
print(f"Secure workspace '{ws_result.name}' created successfully.")
except Exception as e:
print(f"Failed to create workspace: {e}")
By setting public_network_access="Disabled" and hbi_workspace=True, we are adhering to strict compliance standards. HBI (High Business Impact) mode ensures that local scratch disks on compute nodes are encrypted, preventing data leakage if physical hardware is compromised or improperly decommissioned.
Section 2: Identity Management and Secret Rotation
Hardcoded credentials are the bane of security engineering. In the context of TensorFlow News or PyTorch News tutorials, you often see API keys pasted directly into code blocks. In a production environment managed by Azure Machine Learning, this practice is catastrophic. The “silent threat” here is the persistence of credentials in logs, run histories, and version control systems.
Managed Identities over Service Principals
Azure advocates for the use of Managed Identities. Unlike Service Principals, which require you to manage and rotate secrets, Managed Identities are automatically managed by Entra ID (formerly Azure AD). When a training job runs on a Compute Cluster, it uses this identity to authenticate against storage or other services like Azure OpenAI News endpoints.
However, simply using Managed Identity isn’t enough; you must enforce the Principle of Least Privilege. A compute cluster used for data preprocessing should not have write access to the model registry. Similarly, a cluster used for AutoML News experiments should not have administrative rights over the workspace.
Securely Accessing Secrets in Training Scripts
When you need to access external services—perhaps pulling data from Snowflake Cortex News or logging metrics to Weights & Biases News—you should store those API keys in Azure Key Vault and retrieve them at runtime using the Managed Identity.
Here is how to securely retrieve secrets within a training script without ever exposing them in the code or environment variables:
# This script runs INSIDE the training job on the compute cluster
import os
from azure.keyvault.secrets import SecretClient
from azure.identity import DefaultAzureCredential
import mlflow
def get_secret_securely(vault_url, secret_name):
"""
Retrieves a secret from Key Vault using the Compute Instance's
Managed Identity. No hardcoded keys required.
"""
try:
# DefaultAzureCredential automatically uses the Managed Identity
# assigned to the AML Compute Cluster
credential = DefaultAzureCredential()
client = SecretClient(vault_url=vault_url, credential=credential)
retrieved_secret = client.get_secret(secret_name)
return retrieved_secret.value
except Exception as e:
print(f"Error retrieving secret: {e}")
raise
def main():
# Example: Retrieving a WandB API key for experiment tracking
key_vault_url = "https://kv-secure-mlops.vault.azure.net/"
wandb_secret_name = "wandb-api-key"
print("Attempting to retrieve secrets...")
wandb_key = get_secret_securely(key_vault_url, wandb_secret_name)
# Initialize tracking (example with MLflow or WandB)
# Note: We do not print the key to stdout!
os.environ["WANDB_API_KEY"] = wandb_key
# Proceed with training logic (e.g., loading PyTorch/TensorFlow models)
print("Secrets retrieved. Starting training pipeline...")
# ... training code ...
if __name__ == "__main__":
main()
This pattern is essential for integrating with third-party tools mentioned in Comet ML News, ClearML News, and LangChain News. It ensures that even if the training logs are intercepted, the credentials remain secure.
Section 3: Advanced Techniques – Securing the Supply Chain and Inference
The security of your ML pipeline extends beyond the infrastructure to the software supply chain. With the rise of Hugging Face Transformers News and LlamaFactory News, developers frequently pull pre-trained models and containers from public repositories. A “silent threat” in this domain is the use of compromised base images or malicious model weights (pickles) that execute code upon loading.
Container Security and Custom Environments
Azure Machine Learning allows you to bring your own containers. To secure this, you should build base images that are scanned for Common Vulnerabilities and Exposures (CVEs) before they are ever pushed to the Azure Container Registry (ACR) connected to your workspace. Tools that integrate with Docker and CI/CD pipelines are vital here.
Furthermore, when deploying models to endpoints (Real-time or Batch), you must sanitize inputs. Whether you are using FastAPI News wrappers or Azure’s native scoring script, injection attacks are possible. This is particularly relevant for Generative AI applications involving OpenAI News or Anthropic News models, where prompt injection can bypass safety guardrails.
Code Example: Enforcing Secure Compute Configuration
Below is an advanced configuration script that creates a compute cluster specifically designed to reject SSH access and disable local authentication, forcing all access through Azure AD. This mitigates the risk of brute-force attacks on open ports.

from azure.ai.ml.entities import AmlCompute, IdentityConfiguration, ManagedIdentityConfiguration
# Define a Compute Cluster with hardened security settings
secure_cluster = AmlCompute(
name="cpu-cluster-secure",
type="amlcompute",
size="STANDARD_DS3_V2",
min_instances=0,
max_instances=4,
location="eastus",
# CRITICAL: Disable SSH access to the nodes
enable_node_public_ip=False,
# Assign a User Assigned Identity for specific resource access
identity=IdentityConfiguration(
type="user_assigned",
user_assigned_identities=[
ManagedIdentityConfiguration(
resource_id="/subscriptions/YOUR_SUB/resourceGroups/YOUR_RG/providers/Microsoft.ManagedIdentity/userAssignedIdentities/id-aml-training"
)
]
)
)
# Function to validate and create
def create_hardened_compute(client, cluster_config):
try:
# Check if compute exists
try:
existing_compute = client.compute.get(cluster_config.name)
print(f"Compute {cluster_config.name} already exists.")
# In a real scenario, you might audit the existing config here
except:
print(f"Creating hardened compute cluster: {cluster_config.name}")
op = client.compute.begin_create_or_update(cluster_config)
print(f"Provisioning status: {op.status()}")
op.wait()
print("Cluster created successfully.")
except Exception as e:
print(f"Compute provisioning failed: {e}")
# Usage (assuming ml_client is initialized as in Section 1)
# create_hardened_compute(ml_client, secure_cluster)
By setting enable_node_public_ip=False, we ensure that the compute nodes are not addressable from the internet. This forces all communication to route through the Azure backbone, a critical requirement for compliance in financial and healthcare sectors using IBM Watson News or DataRobot News alternatives.
Section 4: Best Practices, Auditing, and Governance
Securing an environment is not a one-time task; it is a continuous process. As NVIDIA AI News releases new hardware optimizations or Ray News updates distributed training protocols, the security configuration must adapt. Continuous monitoring and auditing are the final lines of defense against silent threats.
1. Automated Vulnerability Scanning
Integrate tools like Trivy or Azure Defender for Cloud to scan the container images used in your environments. If you are using JAX News or Apache Spark MLlib News libraries, ensure you are pinned to versions that do not have known CVEs.
2. Audit Logs and Monitoring
Enable diagnostic settings on the AML Workspace to send logs to Azure Monitor or Sentinel. You should specifically alert on:
- Creation of Compute Instances with Public IPs.
- Failed authentication attempts to the workspace.
- Access to the model registry from unauthorized IPs.
3. Model Provenance with MLflow
Use MLflow News capabilities integrated into Azure to track exactly which dataset (hash) and code version produced a model. This prevents “model poisoning” where an attacker subtly alters the training data to introduce backdoors. Similar concepts are gaining traction in Dask News and Lakehouse architectures.
4. Network Security Groups (NSGs)
Even within a VNET, use NSGs to restrict traffic. A training cluster usually only needs outbound access to Azure Storage, ACR, and potentially a package repository (PyPI/Conda). It rarely needs broad internet access. Restricting this prevents data exfiltration to unknown servers.
Code Example: Auditing Compute Compliance
The following script can be run as a scheduled DevOps task (e.g., in GitHub Actions or Azure DevOps) to audit your ML workspace and report on non-compliant compute resources.
def audit_workspace_security(ml_client):
"""
Audits the workspace for common security misconfigurations.
"""
print(f"Starting security audit for workspace: {ml_client.workspace_name}")
issues_found = []
# 1. List all compute instances
computes = ml_client.compute.list()
for compute in computes:
# Check for Public IP on Compute Instances
if compute.type == "computeinstance":
# Note: The property path may vary slightly based on SDK version
if hasattr(compute, 'enable_node_public_ip') and compute.enable_node_public_ip:
issues_found.append(f"HIGH RISK: Compute Instance '{compute.name}' has Public IP enabled.")
# Check for SSH access
if hasattr(compute, 'ssh_public_access_enabled') and compute.ssh_public_access_enabled:
issues_found.append(f"MEDIUM RISK: Compute Instance '{compute.name}' has SSH enabled.")
# 2. Check Data Stores (Conceptual)
datastores = ml_client.datastores.list()
for ds in datastores:
if ds.type == "AzureBlob":
# Logic to check if the underlying storage account allows public access
# This usually requires a separate StorageManagementClient
pass
if issues_found:
print("Security Audit Failed. The following issues were detected:")
for issue in issues_found:
print(f" - {issue}")
# In a CI/CD pipeline, you might raise an exception here to fail the build
# raise Exception("Security Audit Failed")
else:
print("Security Audit Passed. No obvious misconfigurations found.")
# Usage
# audit_workspace_security(ml_client)
Conclusion
The landscape of Azure Machine Learning News is vibrant with innovation, but the complexity of managed services introduces security challenges that cannot be ignored. The “silent threats” in MLOps—misconfigured networks, over-privileged identities, and insecure supply chains—are often more dangerous than theoretical adversarial attacks on models because they provide direct access to the enterprise core.
By implementing strict network isolation, leveraging Managed Identities, securing secrets via Key Vault, and continuously auditing your infrastructure using the Azure SDK for Python, you can build a robust defense-in-depth strategy. Whether you are deploying Large Language Models (LLMs) with LangChain News or optimizing traditional regression models with Scikit-Learn, the foundation must be secure.
As we move forward, the integration of security into the ML lifecycle (DevSecMLOps) will cease to be optional. Organizations must treat their ML infrastructure with the same rigor as their production payment gateways. Start by auditing your current workspaces today, disable public access where it isn’t strictly necessary, and ensure that every compute cycle is authenticated, authorized, and accounted for.